Latest News
Courier Software News
Mailroom Software News
Popular Posts
What’s Hot
Signed, sealed, delivered.
With decades of industry knowledge, our in-house experts are always on hand to help.
With decades of industry knowledge, our in-house experts are always on hand to help.
With decades of industry knowledge, our in-house experts are always on hand to help.
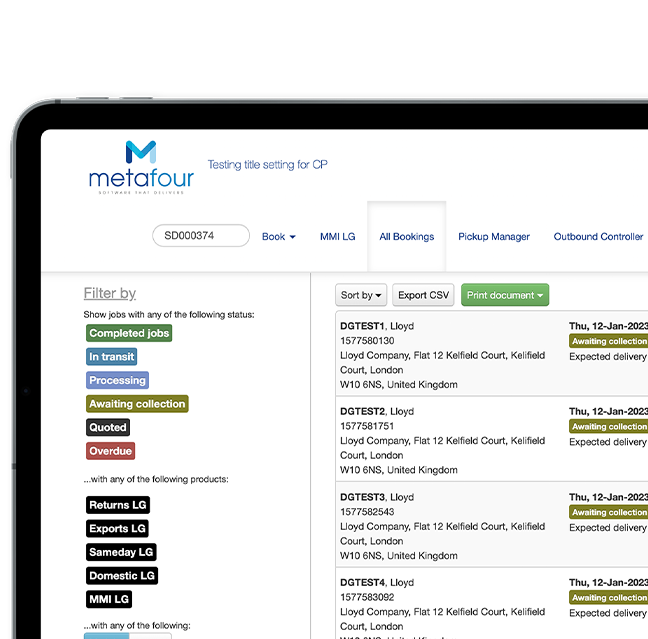
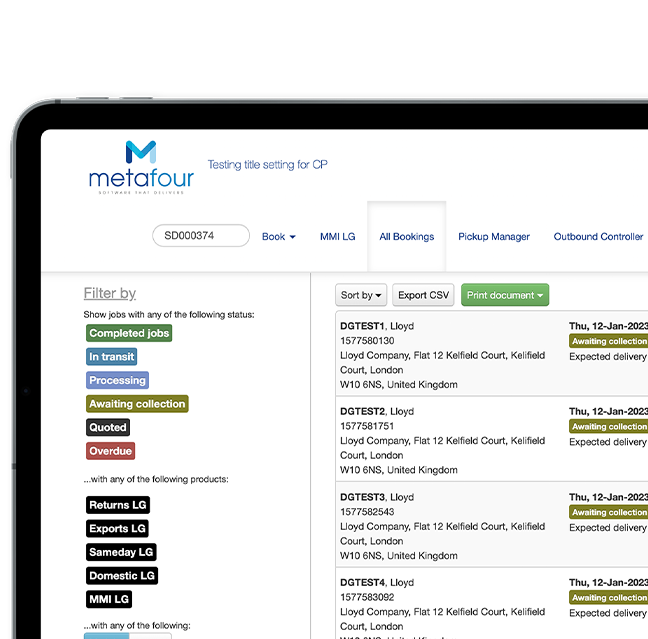
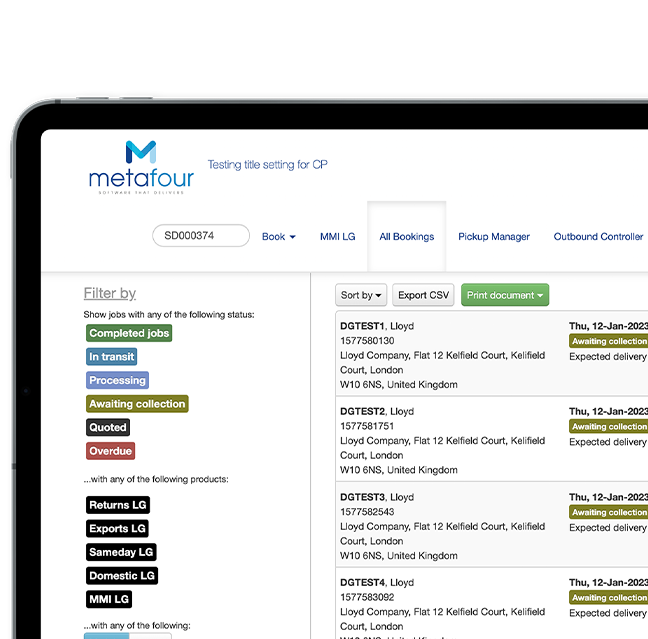
Courier
Industries